The Fiduciary Foundation: Securing Financial Resilience Through a Modern Automation Architecture
Download this strategic blueprint on the Security Architecture of Our Healthcare Automation Solution to enable secure hospital automation, predictable compliance, and durable financial resilience.
Download Free Guide
U.S. Healthcare Operational Pain Points
Administrative complexity in healthcare is being amplified by outdated security models.
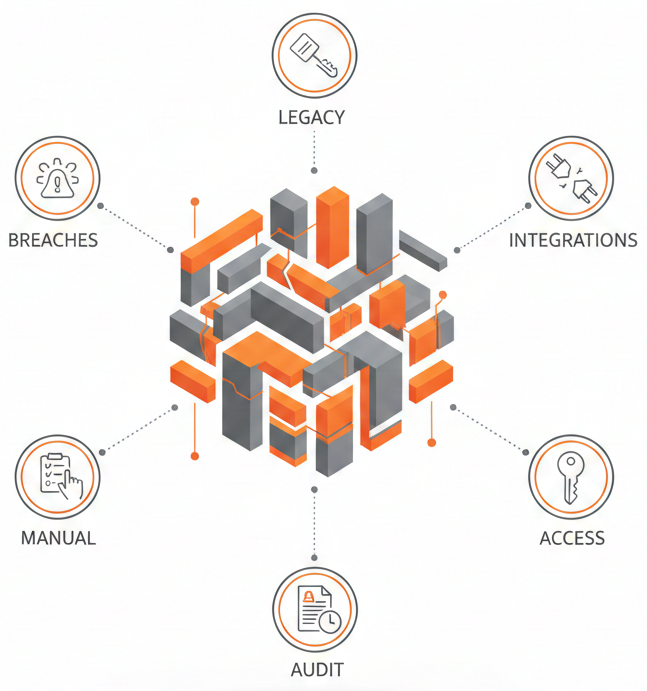
Today’s healthcare leaders are under constant pressure :
Why This Topic Matters Now
Mastering the Security Architecture of Our Healthcare Automation Solution is essential to:
What You’ll Learn Inside the Strategic Blueprint
Download this executive blueprint to understand a layered, defense-in-depth approach to reliable medical billing security, including:
Zero Trust for Automated RCM
Identity & Access Management for AI Agents
Secure Credential Management
Automated Healthcare Security Design
Audit-Ready KPIs
Phased AI Implementation Roadmap
Who Should Read This
This strategic blueprint is designed for healthcare executives who own both financial outcomes and regulatory mandates:
Security Impact: Before vs. After
| Metric | Before Secure Automation | After Secure Architecture |
|---|---|---|
| Audit Log Integrity | Manual, inconsistent, difficult to prove | 100% immutable traceability of all agent actions |
| Over-Permissioning Risk | High, shared access accounts | Zero Trust with least-privilege service identities |
| Time to Audit Readiness | Weeks of manual effort | Real-time, automated compliance validation |
| PHI Exposure Risk | High due to fragmented systems | End-to-end irreversible encryption (in transit & at rest) |
Why ValueDX
ValueDX transforms security from a reactive burden into a strategic financial asset.
We don’t simply automate workflows we architect financial security for hospitals, embedding trust at every layer of the RCM lifecycle.

