The Fiduciary Imperative: Stop PHI Leakage and Secure Your Revenue Cycle
Escalating data breaches demand a new operating architecture for Revenue Cycle Management. Discover why secure automation platforms are now essential to protecting financial integrity, operationalizing HIPAA compliance, and restoring patient trust across healthcare platforms.
Download Free Guide
U.S. Healthcare Operational Pain Points
Healthcare’s administrative complexity has become a systemic vulnerability.
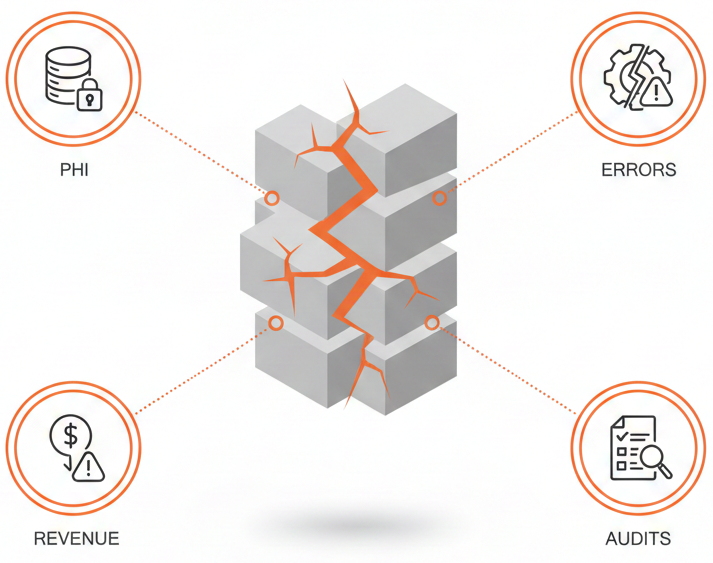
Fragmented workflows, manual data handling, and overly broad user access permissions expose hospitals and health systems to material financial and compliance risk. These gaps result in:
Why This Topic Matters Now
To reduce unplanned compliance costs and sustain scalable RCM performance, organizations must adopt secure healthcare automation solutions that deliver both efficiency and defensible data protection
Healthcare leaders are operating at the intersection of two accelerating forces:
The financial impact of healthcare data breaches and compliance fines is no longer theoretical it directly affects operating margins and enterprise valuation.
What You’ll Learn Inside the Strategic Brief
This executive-level guide provides a practical blueprint for operationalizing security in revenue operations, including:
The Zero Trust Blueprint
The architectural shift required to enable secure, scalable automation across RCM workflows
Eliminating High-Risk Manual Workflows
How to identify and remove human-error data leaks and insecure credential handling
The ROI of Compliance
A financial framework to quantify avoided fines, reduced breach exposure, and lower audit costs
Contextual Access Control
How modern platforms enforce least-privilege PHI access based on role, task, and risk
Measuring Trust
Key KPIs that connect security posture, compliance performance, and revenue outcomes
Who Should Read This
This strategic brief is designed for executive and operational leaders responsible for financial resilience, compliance, and enterprise risk, including
Security Maturity: Before vs. After
| Metric | Before Strategic Implementation | After Secure Architecture |
|---|---|---|
| Annual Breach Cost Exposure | High and Unpredictable | Significantly Reduced (e.g., ~2% exposure) |
| Audit Readiness | Manual and Time-Consuming | Automated, Near Real-Time |
| Data Access Control | Broad Role-Based Access (RBAC) | Fine-Grained, Contextual Access |
| Clean Claims Submission | Vulnerable to Data Errors | Improved via Secure, Verified Data Inputs |
Why ValueDX: Outcomes, Not Tools
ValueDX delivers secure automation for Revenue Cycle Management, built on a Zero Trust foundation.
We help healthcare platforms:

